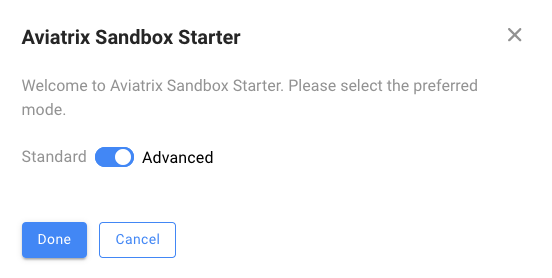
Advance mode is for users who want to change the region, naming convention, and subnet scheme.
Provide AWS Credentials
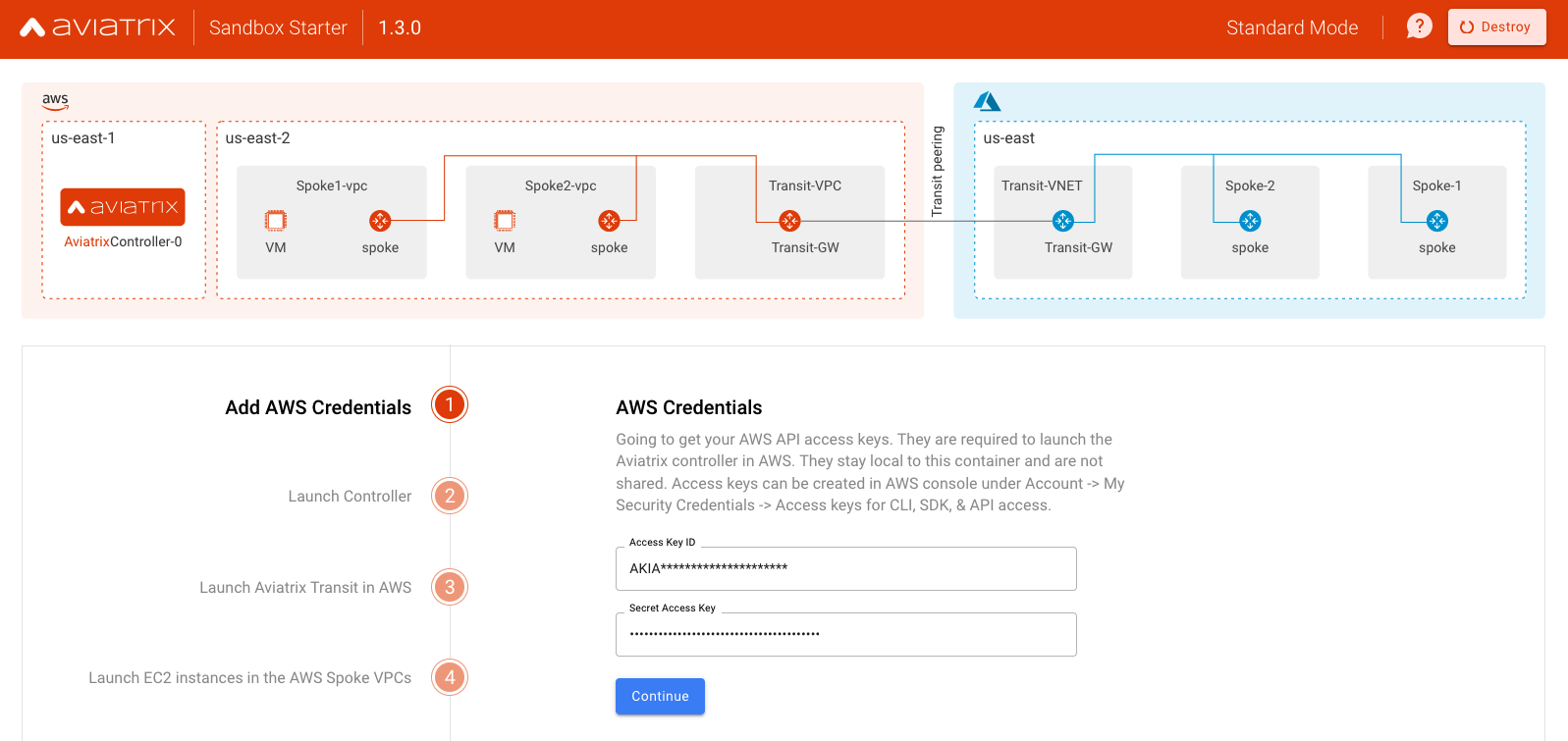
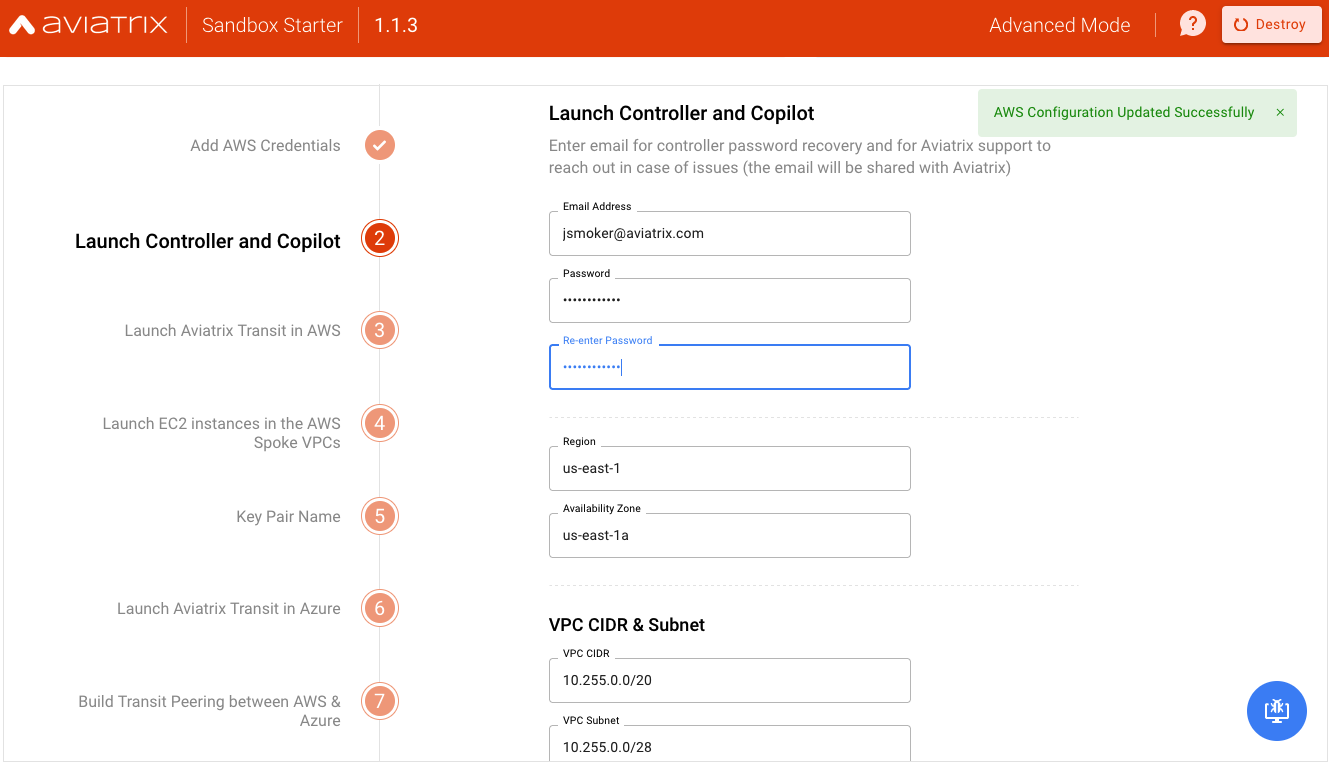
Before launching the controller, you can change the region and subnet details as shown in the following screenshot.
Notes
- Be sure to subscribe to the AWS marketplace offerings mentioned in the Before You Begin section above and set up your account to generate the Controller License required as input.
- In the future, we might add the option to launch Controller in other Clouds
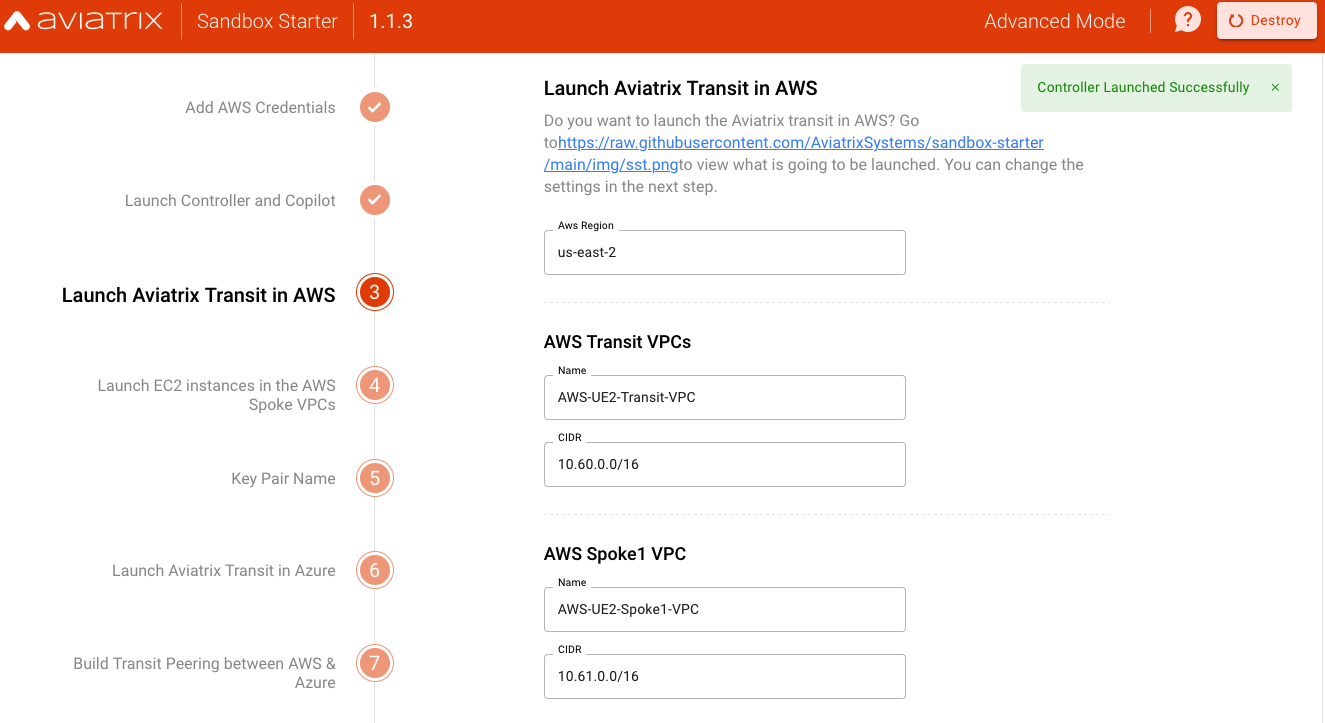
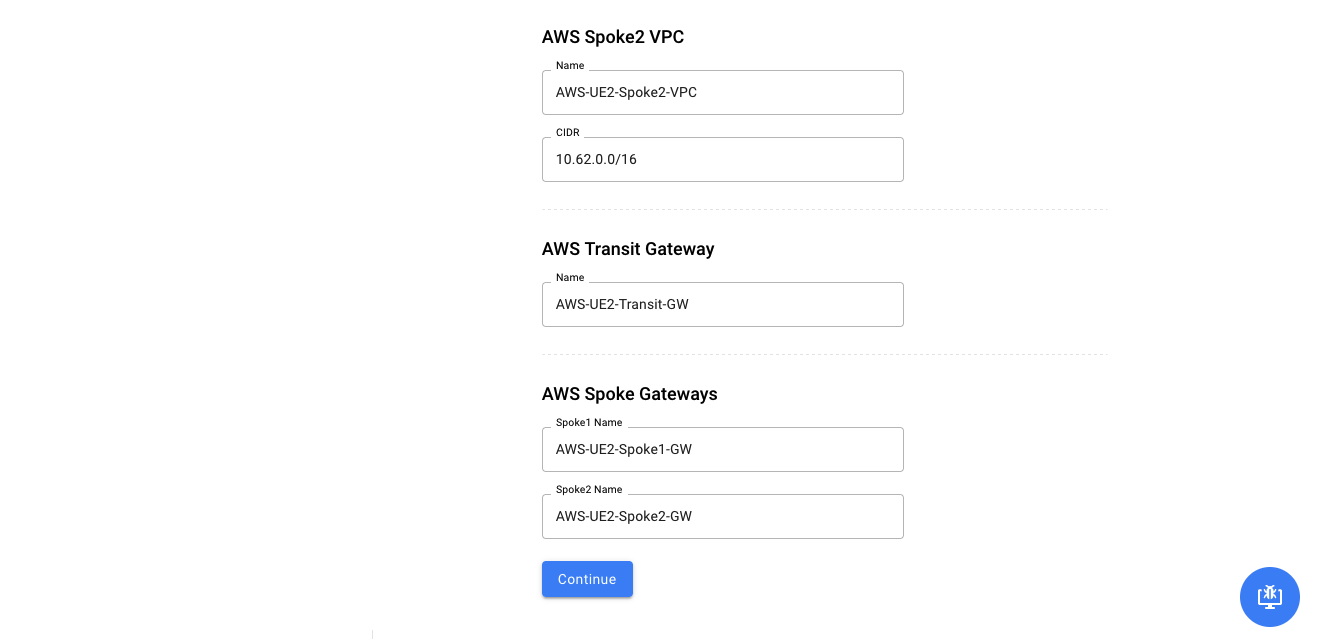
Launch Global Transit (Hub) and two Spokes in AWS
Launch Aviatrix Global Transit (Hub) and two Spokes in the AWS region as per your requirement.
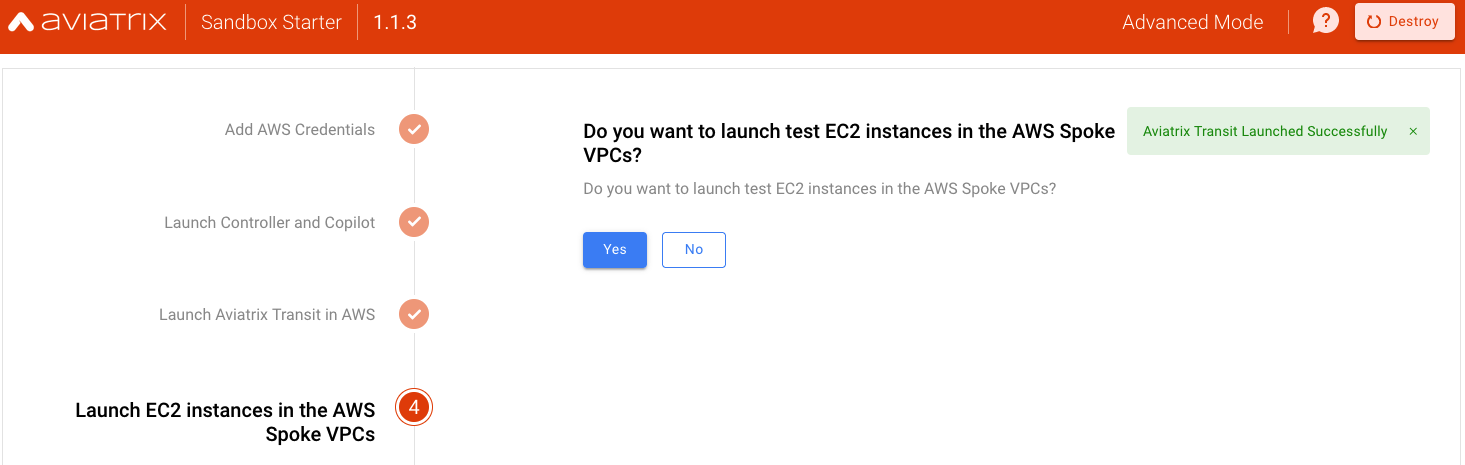
Launch Test EC2 instances
Test EC2 (Amazon Linux VMs) will be launched in their respective Spoke VPCs
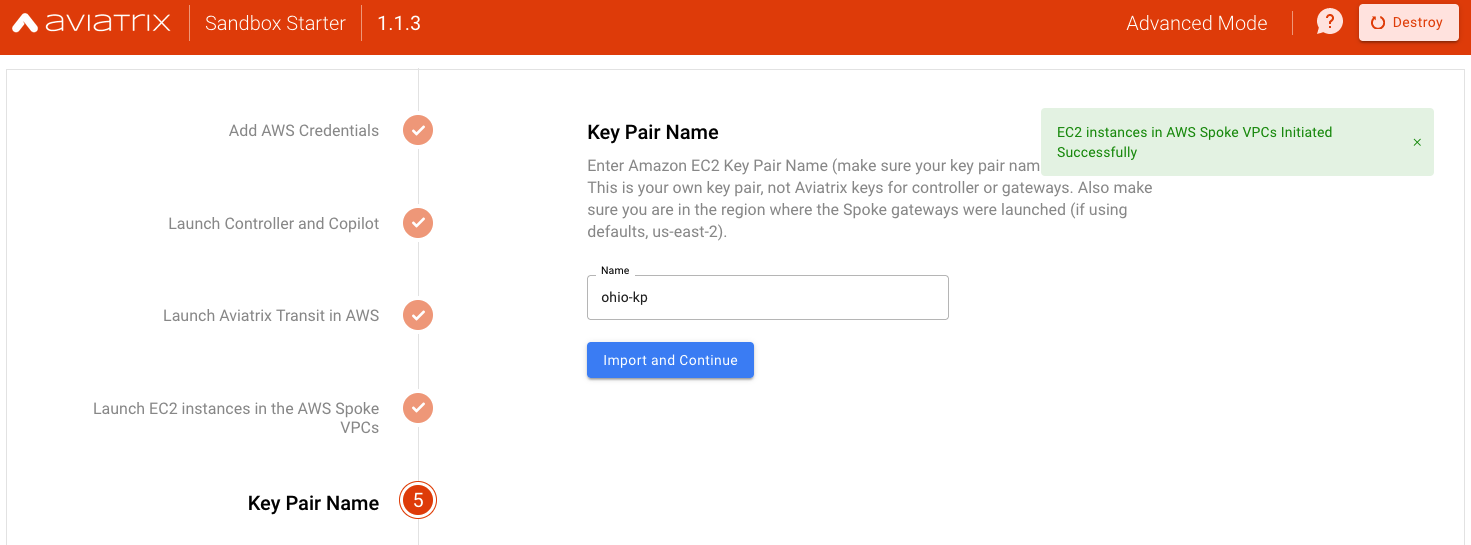
Provide an Existing Key Pair Name
This must be configured in your AWS account in us-east-2 (Ohio) region as per-requisite. You will need this Key Pair to login to test EC2 instances to verify the end-to-end connectivity.
This concludes the deployment in AWS. Optionally you can also deploy Aviatrix Transit network in Azure and provide connectivity between AWS and Azure clouds.
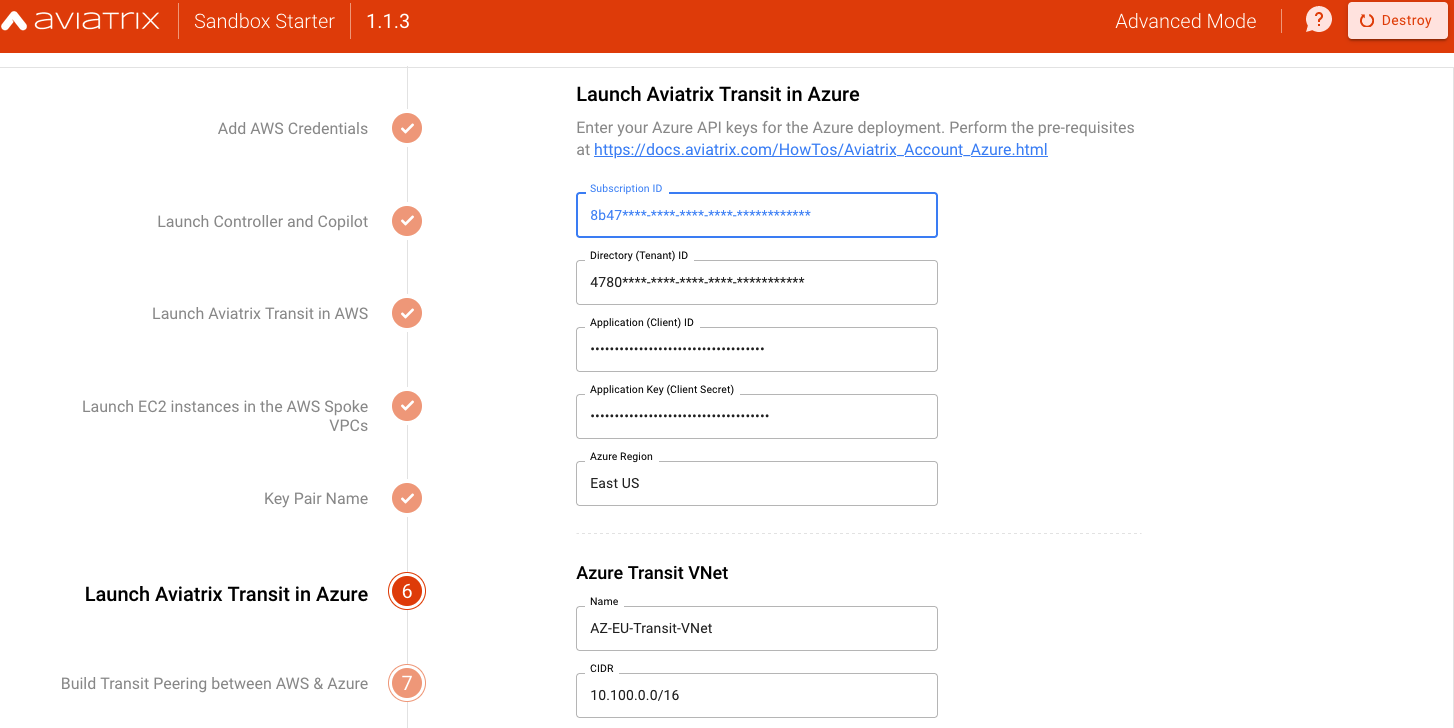
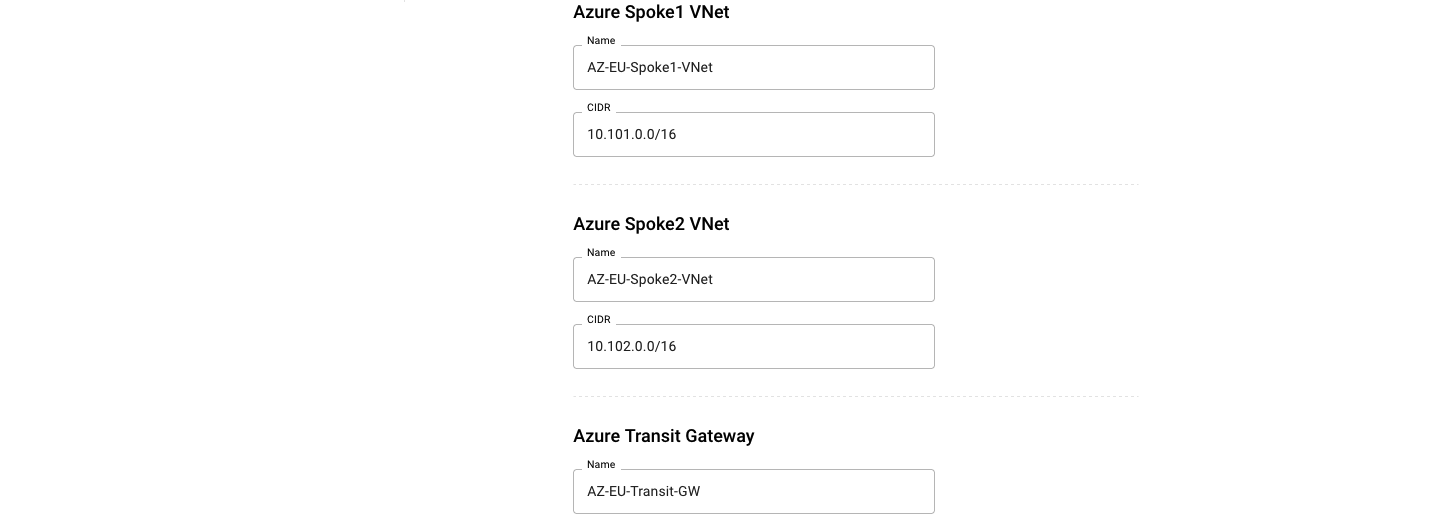
Launch Aviatrix Transit in Azure
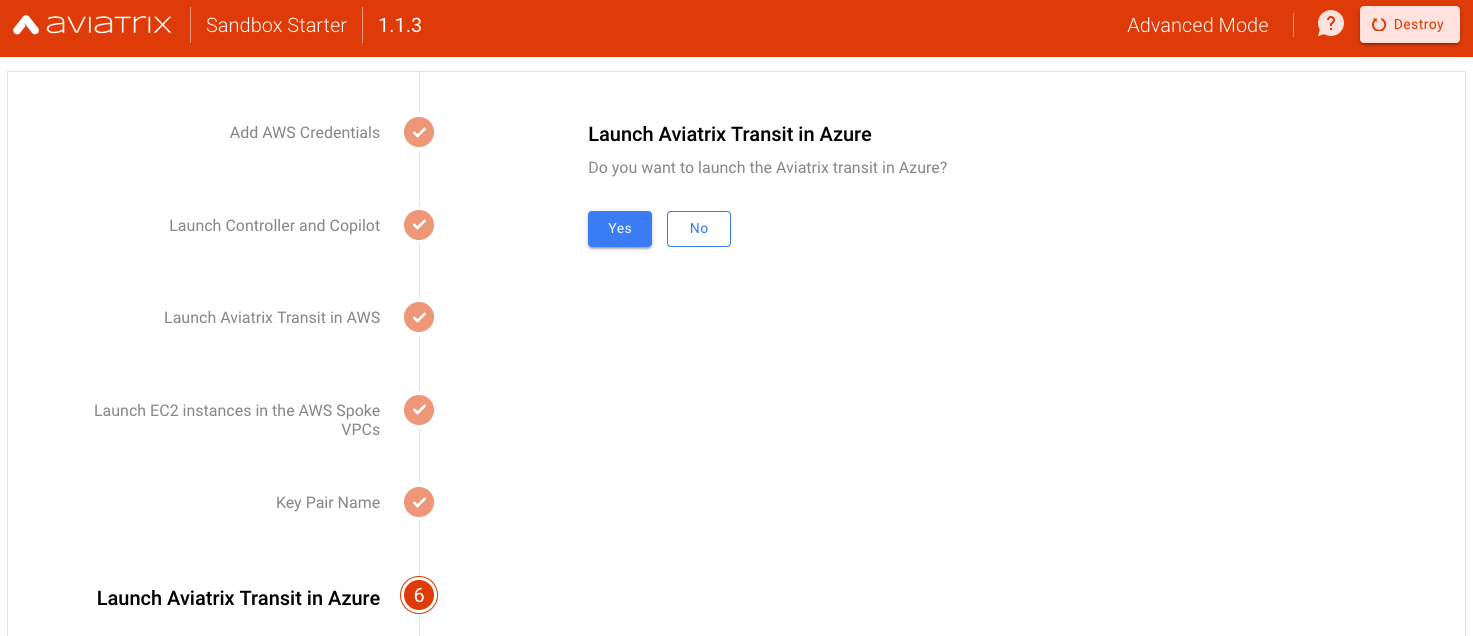
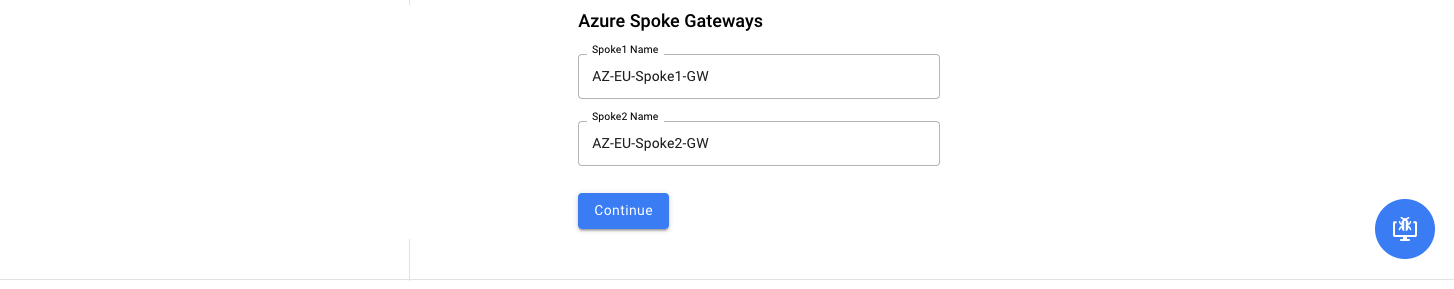
Connect AWS and Azure with a Single Click
Success Screen
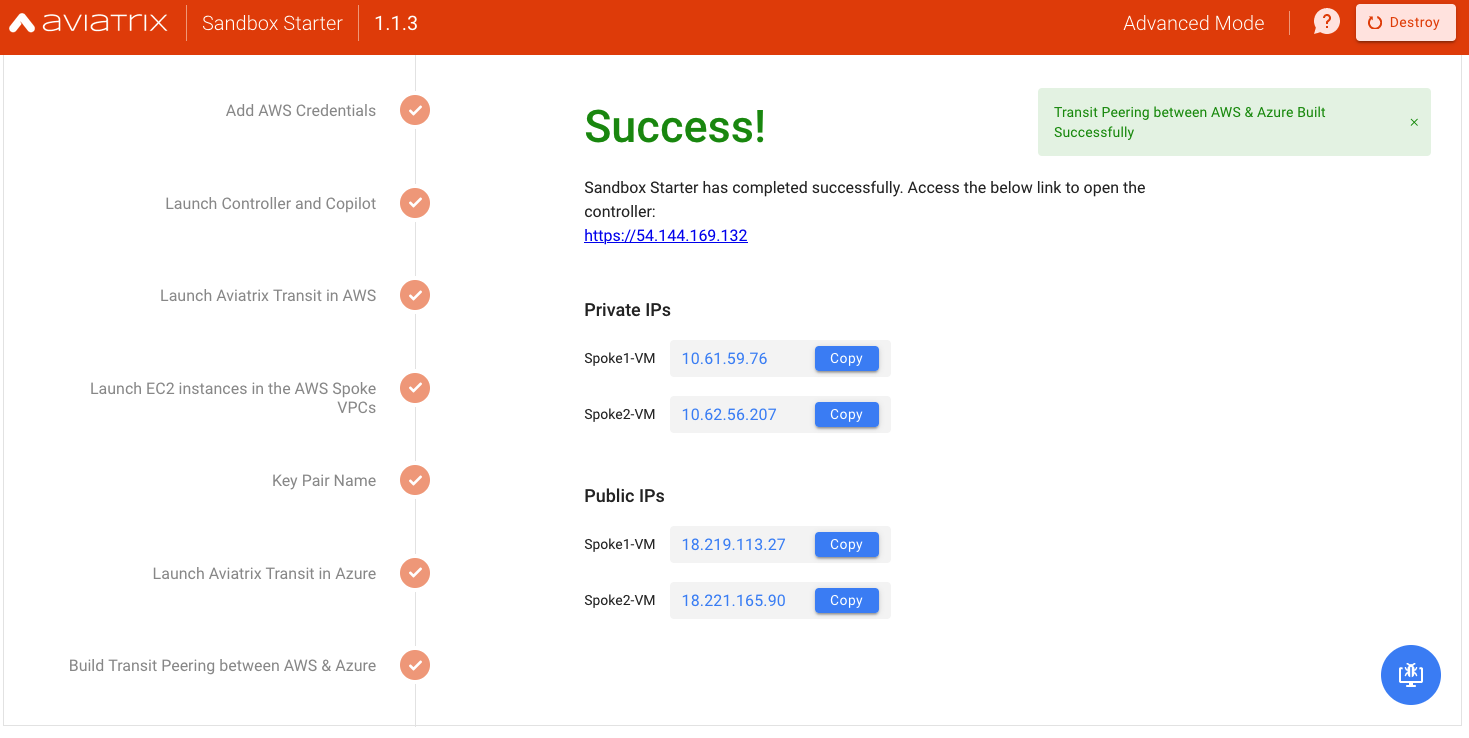
Lock Inbound Access to Controller
After the Controller is deployed, you must do the following to lock the inbound access so that no one has access to it.
1- Enable the security group management feature so all of the gateways’ IP addresses are allowed to reach the controller on HTTPS/port 443
2- Lock all inbound access to Controller except your IP address
Destroy / Delete the entire Sanbox LAB
Once you are done testing and validating Cloud Networks, you may destroy or delete the entire lab. First, turn off AWS access security on the controller by logging into the controller and clicking on “Settings” in the left-hand nav. Click on “Controller,” then “Access Security” in the top tabs. Under “Controller Security Group Management,” click “Disable”.
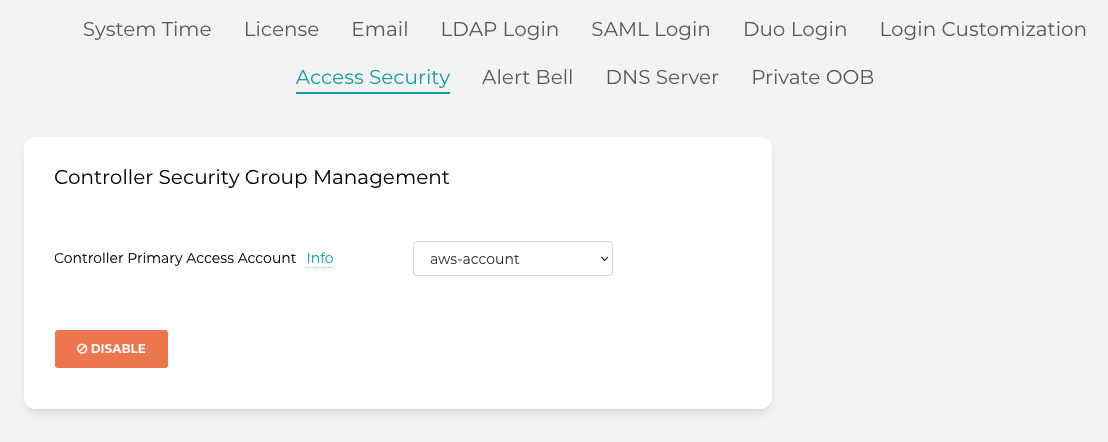
Back in the sandbox starter, use the “Destroy” option on the top right of the browser UI.
If you destroyed SST before getting a chance to destroy your environment, you will need to manually delete these resources in order (always check you are in the appropriate region first):
- Terminate the Spoke and Transit gateways in AWS (if applicable)
- Remove the Resource Groups in Azure (if applicable)
- Disable Termination Protection on the EC2 instance for the Controller
- Terminate the Controller EC2 instance
- Remove the SSH keypair
- Delete the Security Groups
- Delete the VPC where the Gateways and Controller was deployed
- Delete the IAM Roles and Policies starting with ‘aviatrix’
Note that if you deployed CoPilot, it must be deleted manually by logging into AWS/Azure Console.
Support Model
This community-based and open-source tool is NOT supported by the Aviatrix Enterprise support team. For any questions or issues related to this tool, please use the Aviatrix Community platform.
Open Source
- Code for this open-source tool is available at https://github.com/AviatrixSystems/sandbox-starter
- Terraform module for Sandbox Starter launch is available here at https://github.com/terraform-aviatrix-modules/terraform-aviatrix-aws-sandbox-starter
- The container code is available here
Comments are closed